Hello, friends. Today’s post is going to be a little more ranty than normal; feel free to skip if you like. My day job involves cybersecurity, and in this field it is commonplace for organizations to over-state the security benefit of their certifications. Keep in mind that all of these different certifications do add value, but they don’t always add value for all parties involved equally. If you work in the field, please understand that I am writing this for non-practitioners.
PCI is an acronym for “Payment Card Industry,” and it’s important you know that as that is the primary beneficiary of the PCI certification. DSS is an acronym for “Data Security Standard,” and this is the standard against which systems are certified by PCI. This certification primarily covers two things: card data and user authentication data which could give someone access to card data. When I say card data I specifically mean:
- The card number
- The expiration date
- The 3-to-4 digit code that you’re often asked for
When I say user authentication data I mean:
- Password
- Any secondary factors such as a time-based one-time-password (TOTP, the little code your bank texts you when you’re trying to log in)
- Note that the email address and username are not included
These standards exist to reduce business risk to the payment card industry, making it less likely that financial institutions and card networks will experience losses due to fraud or other security problems. While the rhetoric around PCI audits is often very reassuring and safe-sounding, it is crucial for end-users (people using the system, not the businesses providing the system) to understand that this certification does not protect you any farther than your credit card number.
Scope management
Audits are expensive, and doing the work necessary to improve systems to sustain an audit is even more expensive, so most security frameworks have a flexible set of rules around what is “in-scope.” If a business has a website which combines both really interesting articles about coffee, but also sells coffee (and who wouldn’t want to sell coffee?!), they’re not going to want to do the work of hardening and auditing their WordPress install alongside their e-commerce app. Matter of fact, they may not even want to audit the entire e-commerce app! I’ve seen organizations limit their PCI audit to just the checkout and login functionality, which is perfectly fine under PCI.
This means that the warehouse integrations (almost always plural), coupon system, profile management, content management system, and customer service systems are likely out-of-scope. Every organization will draw this in-scope line differently, but I’ve never seen an organization consider their entire application in-scope, not even when I worked for a company whose business was just credit card processing (they kept the check processing side separate).
Why scope matters to users
While it is genuinely wonderful that PCI protects your cardholder data, there is so much left on the table. Here are all of the information types not required to be in-scope for PCI:
- Full legal name
- Physical or mailing address
- Phone number
- Email address
- User information linked to other third-party systems (like social media user names)
- Checking and savings account numbers
- Government ID numbers (SSN, Passport Number)
- Location data
- Search history
- Purchasing history
- Your contacts list
- Biometric information like Face ID, Touch ID, or facial recognition information
When you look at the giant pile of highly sensitive user data present here it’s easy to see how this certification will not protect end users. If a web application is PCI certified, it could still lead to scams, stalking, financial fraud, and even identity theft; PCI does not protect users.
A common practice for organizations which must comply with PCI is to construct entirely separate infrastructure for the login system and the checkout page, and then limit scope to just that. This means that they obtain their certification without the auditor ever reviewing any part of the system beyond those limited systems. This reduces the value of that certification to the user as literally every other part of the system is excluded from the audit.
But that’s not what PCI is for; why bring it up?
I hear all of my colleagues and fellow hackers in the non-existent comments: but this isn’t what PCI is for! They’re right. PCI is a narrowly-scoped certification to make sure that businesses are taking reasonable measures to protect the data security for systems involved in the processing of payment card transactions; nothing more. So why am I bringing this up? Let’s go on a user-experience journey I’ve had recently, and I hope by the end you’ll understand.
As enshittification progresses, companies have increasingly started moving functionality into areas where they can demand users to disclose more valuable sensitive information. In the United States, where the collection and sale of user data is not at all prohibited and consent is not required (except in limited jurisdictions based on physical location, which totally makes sense on the internet right?), companies can collect a fee from merchants during a sale while also requiring users to use a mobile phone app in order to track shipping information. This is precisely what Shopify is doing.
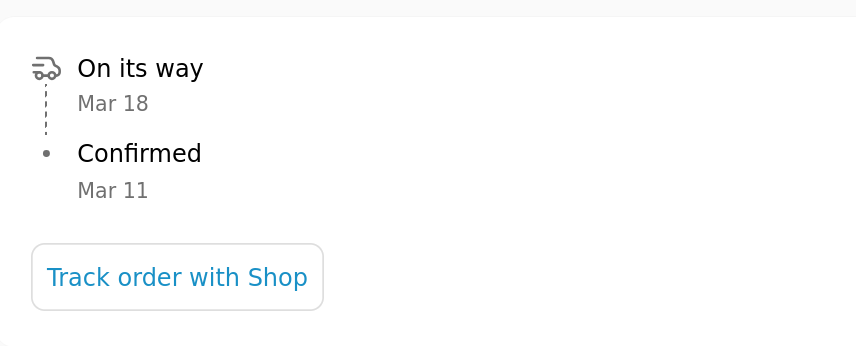
Shopify supplies other folks’ e-commerce customers with an easy-to-use express checkout option which makes it easier and more secure to check out on several sites. Once you look at your receipt, though, you’ll see a “Track order with Shop” when your order has shipped, but they won’t disclose the tracking information outside of the app. If you click the button, it gives you a QR code to download and run a mobile app.
So in order for me to track this order I have to download and use their app from the Apple App Store. Why not show me the tracking information? Shop assures me that this is so in order to maintain the “mobile-first experience.” This is really interesting, though, because as most companies out there the mobile-first experience is actually a web-first experience locked in the prison of a mobile phone app, and we know this because Shopify has been very clear that they use React Native for mobile app development.
React Native is a set of libraries which allow you to take your website code and convert it into a mobile phone app for Android and iOS with minimal code changes. It’s really powerful and it has helped a number of developers reuse code in interesting ways that save time and protect the user experience. It allows them to maintain theming and branding, preserve graphics that are important to user functionality, and it drastically reduces the number of problems that are limited to only one platform. It does, however, mean that there really isn’t a “mobile-first” component, as the purpose of React Native is to abstract away the mobile handset itself, and to stick the web app inside of a mobile app shell; it’s still using all of the same web technologies. So why would a company produce an app with web technologies, limit the web-visible side and force people into a mobile app?
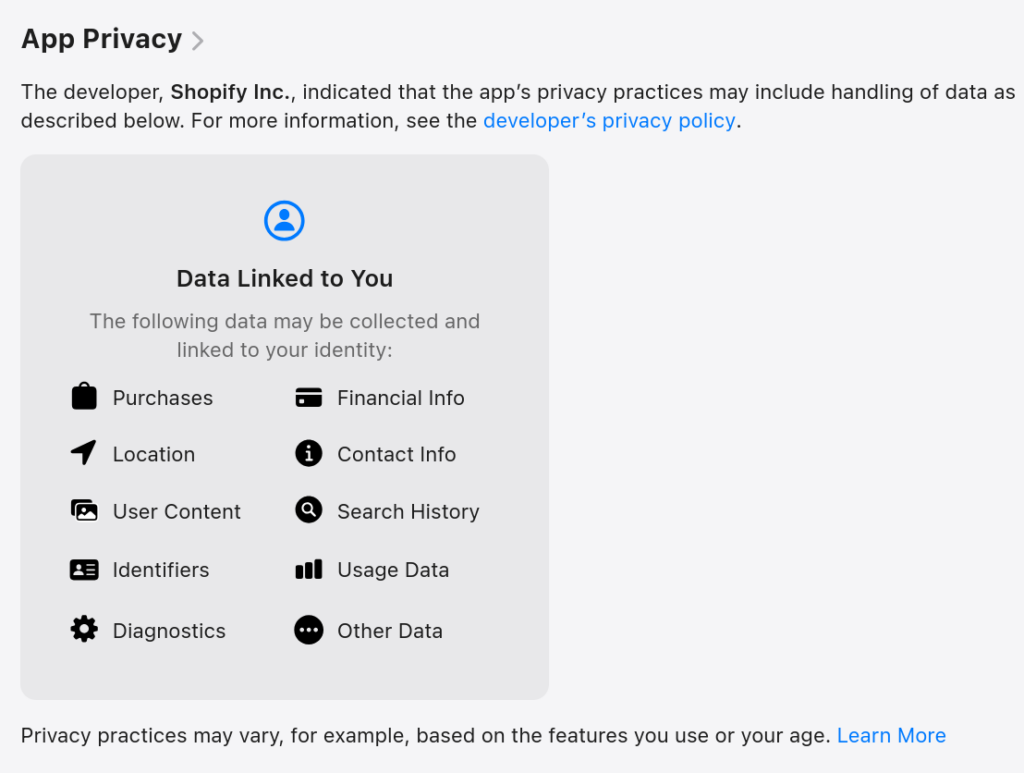
Mobile apps can be controlled by the developer, bypassing browser-based security and privacy settings. Using this approach, Shopify can require you to give them a bunch of data that is valuable. This data is then either packaged and sold by the company, or used by that company to provide additional services to business customers such as targeted marketing and advertisements. Shopify’s privacy policy makes room for this line of business explicitly when they say they can use your personal information “[t]o market, advertise, and promote Shopify and Merchants on and off Shopify, including for personalized communications or advertisements relating to Shopify and Merchants on third-party services.”
This means that Shop is collecting your data on and offline, any time they can correlate a data point to your activity. Forget to close the Shop app? It could be tracking your location as you walk around. This allows them to correlate your online and offline shopping habits, and that is very creepy but very valuable to these companies.
All of this is to say that there’s no reason why Shopify can’t put the tracking information on their website and also offer the mobile app for those who want it. They only require the use of the mobile app because they wish to collect this valuable information for their own business purposes which add zero value to users.
I know that I’m picking on Shopify here, but they’re far from the only bad actor here, and they’re far from the worst. Shopify, to their credit, offers you an opt-out regardless of where you live (unlike CrunchyRoll whose parent company Sony will only allow you to opt out if you live in a state which requires them to). While it is unquestionably a good thing that they offer this opt-out, they’re clearly still participating in this user data marketplace and I don’t think that’s OK.
Why is it a problem?
While the creepy factor is one I have a hard time putting down, there are other problems here as well. It’s March of 2026, and I’ve already received four letters in the mail this year related to security breaches. These are companies that I’ve done business with but who have experienced a data breach, meaning more and more of my personal data is being leaked to scammers and dipshits online. This means more scam attempts, more unwanted attention from threat actors, and also more junk mail, telemarketers, and government surveillance.
The FBI has now publicly acknowledged that it is purchasing user data from private companies and using it for surveillance purposes. This means that when you buy something online, or use identity verification services, or just read an article on a site with a bunch of ads, you could be contributing to a profile that the FBI constructs regardless of Fourth Amendment protections. DHS/ICE has also been doing this, and it has already been used to attack individuals exercising their First Amendment rights and to hunt down targeted minorities for government harassment, detention, and expulsion without due process of law.
What can we do about it?
Complain. Complain to merchants, and complain to your elected representatives. While some companies will respond and do better, that’s not a sustainable path to regaining our privacy: we need policy solutions which go beyond regulating security and user control of their own data.
We have seen a number of data regulation regimes over the last decade, but there’s one thing we haven’t yet seen take hold: anti-enshittification measures. We need policies which require companies to accommodate users who wish to retain their privacy, and we need limits on what information companies can harvest from users without their knowledge and consent. We need requirements that vendors must be disclosed, and that their security and privacy practices are compatible with the applications which depend on them.
It’s been more than thirty years of unregulated ad-tech on the internet, and despite all of the promises of self-regulation and the concerns about regulations stifling innovation, we now know better. Limiting the collection and indefinite storage of user data only stifles the variety of innovation that harms users, and these companies will never regulate themselves with users in mind.
Wait, why were we talking about PCI?
Yesterday I reached out to Shop app folks and complained that I couldn’t access tracking information without their app. Their response was to tell me that there’s nothing to worry about, that they are PCI certified, and I can rest assured that my information is safe with them. These fine people, and I mean that, likely don’t understand that what they’re saying is non-responsive to my objections. A PCI audit is as relevant to my privacy concerns as a kitten is to the manufacture of industrial lathes in Taiwan, but it sounds reassuring and it’s probably in their customer service script for that reason.
I wrote this post mostly to process, but also to make sure folks understand that from the perspective of the end-user, a PCI certification adds little value over a modestly reduced likelihood that your card number won’t be stolen. Businesses are required by the terms of their merchant agreements to comply with PCI. It doesn’t make the organization more trustworthy, it doesn’t protect your privacy, and it’s not even a signal that they take security seriously.
Thanks for joining me for this opinionated journey.